Security for products and industrial applications
The Product Protection and Industrial Security department develops security solutions and new methods for securing electronic devices and for protecting corporate assets. To this end, our scientists study security issues in the fields of product protection, automotive security, industrial security, and the Internet of Things.
We support manufacturers of components, devices and vehicles, as well as suppliers and system integrators in developing, implementing and integrating secure vehicle and device functions, applications and value-added services.
For our customers, we offer security risk assessments to identify and manage threats, as well as methods and tools to systematically identify conceptual security vulnerabilities at an early stage. Furthermore, we support our customers in initiating the appropriate countermeasures.
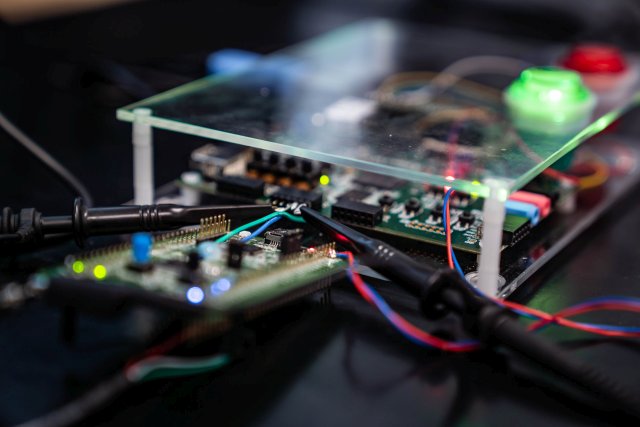
Fraunhofer AISEC operates modern test laboratories for performing security, compliance, and interoperability tests. This allows us to offer a comprehensive, independent security evaluation of connected and embedded systems as well as hardware and software products.
 Fraunhofer Institute for Applied and Integrated Security
Fraunhofer Institute for Applied and Integrated Security